From Newbie to Pro: My Journey to a $3,000 Bug Bounty
From Newbie to Pro: A Developer’s Path to a $3,000 Bug Bounty My journey in the realm of cybersecurity started with a simple curiosity about how applications are built and…
Security and Vulnerability Management Global Market Analysis, Trends, Growth, Research And Forecast 2033
Global Security and Vulnerability Management Market Analysis: Insights for Developers The Business Research Company has recently unveiled a detailed report on the Global Security and Vulnerability Management Market, projecting key…
The FBI wants you to stop texting without encryption. Here’s why.
The FBI Urges Encrypted Messaging: A Developer’s Perspective In a significant push for cybersecurity, the FBI, in partnership with the Cybersecurity and Infrastructure Security Agency (CISA), is urging individuals and…
Deloitte Data Breach: Company Denies The Breach Says, “Only Single Client System Affected”
Deloitte UK has firmly dismissed allegations from the ransomware group Brain Cipher regarding a significant cybersecurity breach, stating that only a single client system was affected. This incident underscores critical…
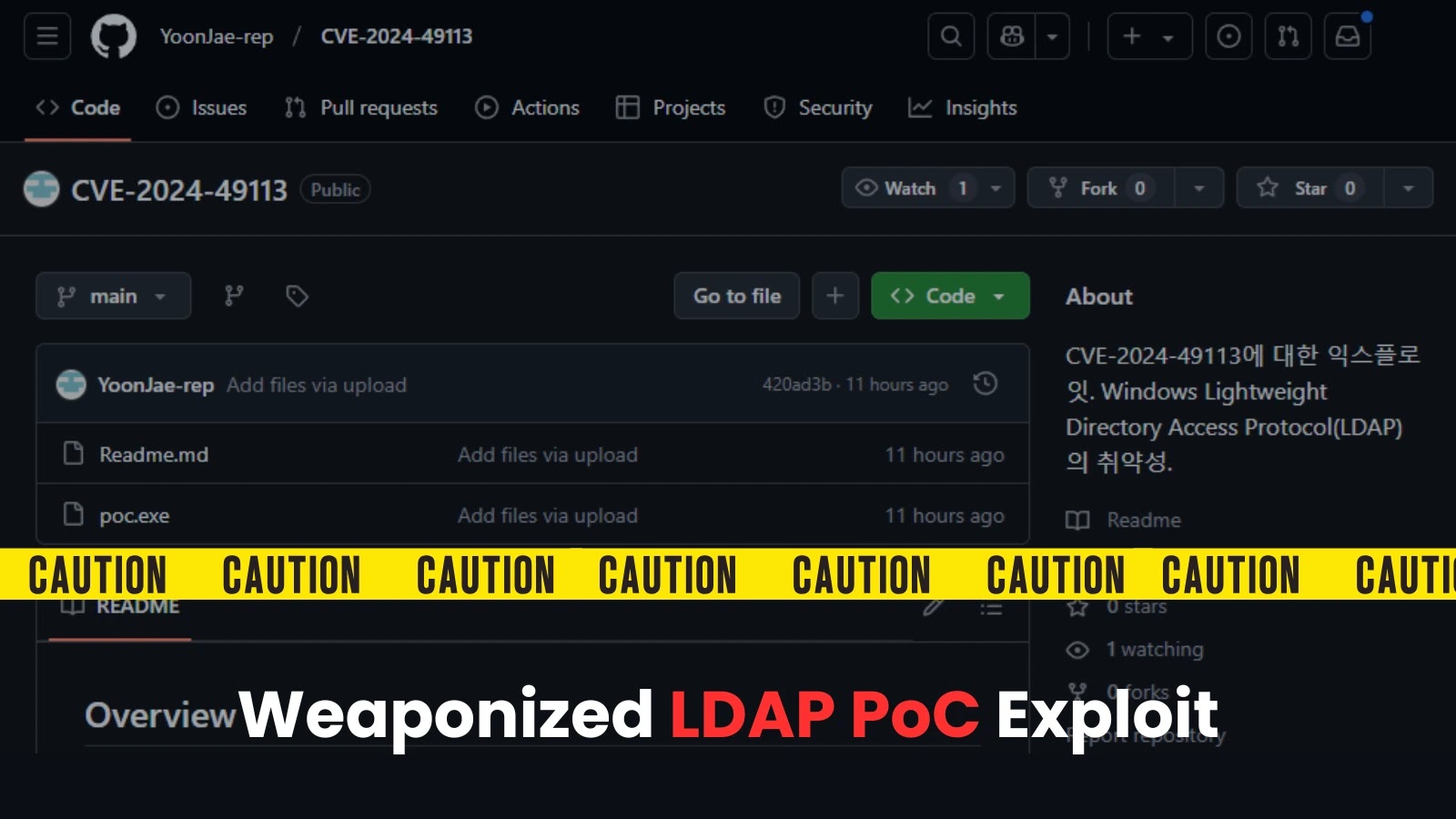
DaMAgeCard: A New Attack Exploits SD Cards to Compromise System Memory
The DaMAgeCard attack represents a significant threat vector for developers and organizations utilizing devices that accept SD cards, particularly those adhering to the SD Express standard. This emerging vulnerability allows…
Justin Reock
Justin Reock is recognized as an influential voice in the cloud-native ecosystem, driving innovation through his deep understanding of modern software practices. Developers looking to enhance their skills and understanding…
Salesforce revamps Heroku PaaS for Kubernetes, .NET
Salesforce has announced significant updates to the Heroku Platform-as-a-Service (PaaS) at the recent AWS re:Invent event. The revamped Heroku now prominently supports .NET and Kubernetes, addressing a growing demand among…
Heroku platform announces fully cloud-native service
In a significant move towards modernization, Heroku has announced the full adoption of a cloud-native service architecture, primarily powered by Kubernetes. At an event underscored by advancements in technologies like…
Five ways to tighten up Kubernetes security
Five Ways to Tighten Up Kubernetes Security Kubernetes is poised to be the prominent platform for GenAI applications by 2025, emphasizing the necessity of robust security practices for developers working…
Explosive Growth in the Container and Kubernetes Security Market: Trends, Industry Challenges and Future Outlook to 2030
The container and Kubernetes security market is witnessing a significant transformation as businesses increasingly adopt cloud-native architectures. This shift not only modernizes their infrastructure but also brings to the forefront…
 Exploitation of New Ivanti VPN Zero-Day Linked to Chinese Cyberspies
Exploitation of New Ivanti VPN Zero-Day Linked to Chinese Cyberspies Palo Alto Networks Patches High-Severity Vulnerability in Retired Migration Tool
Palo Alto Networks Patches High-Severity Vulnerability in Retired Migration Tool Kerio Control Firewall Vulnerability Allows 1-Click Remote Code Execution
Kerio Control Firewall Vulnerability Allows 1-Click Remote Code Execution Ivanti patches actively exploited zero-day.
Ivanti patches actively exploited zero-day. Major Vulnerabilities Patched in SonicWall, Palo Alto Expedition, and Aviatrix Controllers
Major Vulnerabilities Patched in SonicWall, Palo Alto Expedition, and Aviatrix Controllers Chinese-linked Hackers May Be Exploiting Latest Ivanti Vulnerability
Chinese-linked Hackers May Be Exploiting Latest Ivanti Vulnerability Biden’s final cyber order tackles digital weaknesses.
Biden’s final cyber order tackles digital weaknesses.