The Linux Foundation launches an initiative to support open-source Chromium-based browsers
Google’s Chromium source code will serve as the foundation for an array of new open-source web browsers, as part of an initiative by The Linux Foundation. The Linux Foundation has…
Mazda Connect Systems Vulnerable to Cyber Attacks
Recent findings reveal that unpatched vulnerabilities in the Mazda Connect system could expose vehicles to significant cyber security threats. These vulnerabilities allow attackers to install persistent malware, potentially granting them…
Mirai Botnet Variant Exploits Four-Faith Router Vulnerability for DDoS Attacks
A new variant of the Mirai botnet has been identified exploiting a critical vulnerability in Four-Faith routers, specifically CVE-2024-12856. This exploit enables attackers to launch Distributed Denial-of-Service (DDoS) attacks with…
US Launches Cyber Trust Mark for IoT Devices
The introduction of the Cyber Trust Mark by the U.S. government signals an important shift in how cybersecurity is perceived in the realm of Internet of Things (IoT) devices. This…
AWS Repeats Same Critical RCE Vulnerability 3 Times in 4 Years
In a troubling trend that may concern developers leveraging Amazon Web Services (AWS), a critical remote code execution (RCE) vulnerability has reoccurred within AWS’s Neuron SDK three times over the…
MediaTek says ‘Happy New Year’ with critical RCE, other bugs
MediaTek Says ‘Happy New Year’ with Critical RCE, Other Bugs MediaTek Says ‘Happy New Year’ with Critical RCE, Other Bugs As the new year begins, MediaTek has drawn attention for…
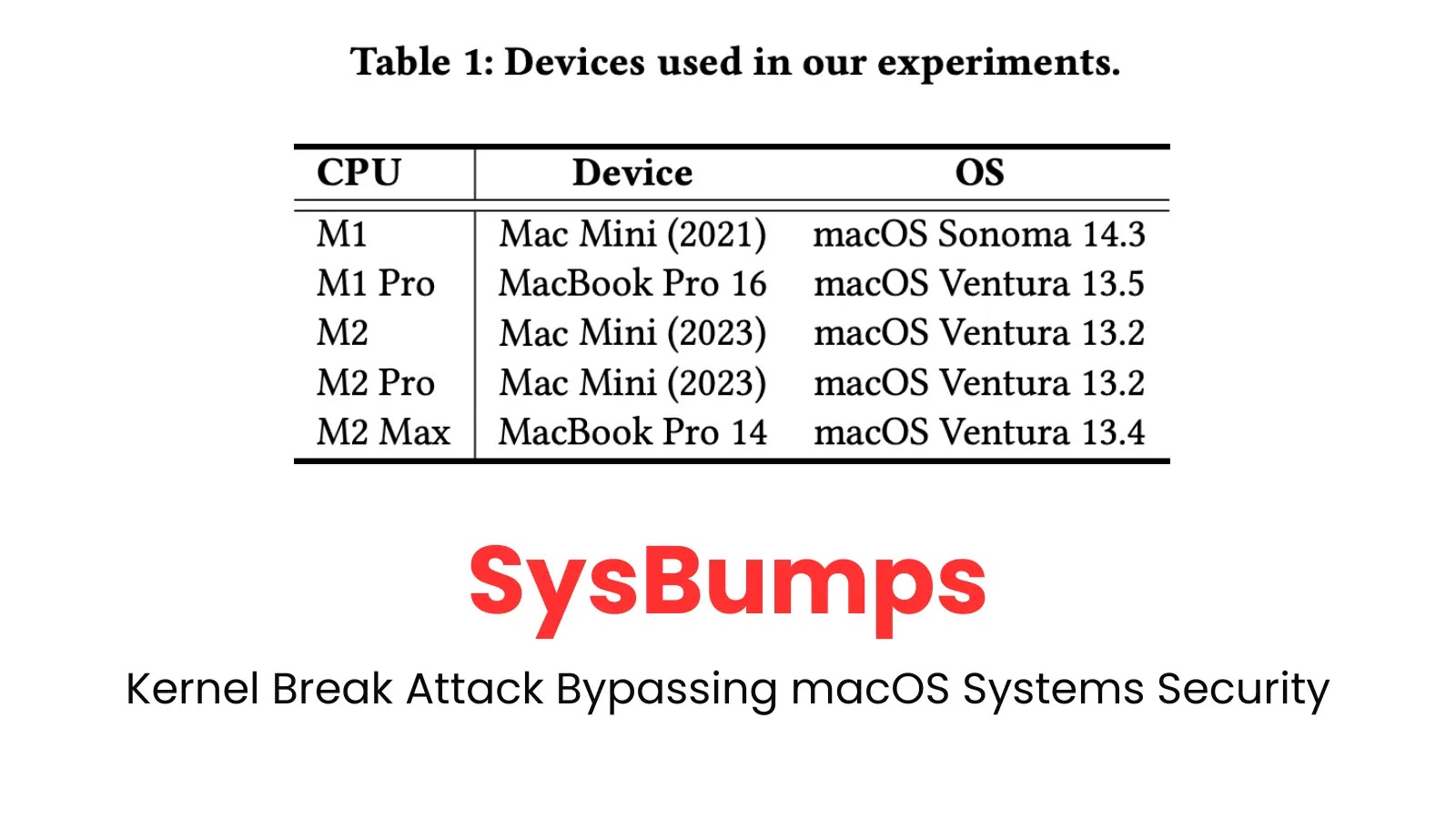
SysBumps – New Kernel Break Attack Bypassing macOS Systems Security
Recent findings from security researchers reveal SysBumps, a sophisticated attack vector targeting macOS systems equipped with Apple Silicon processors. This method exploits speculative execution vulnerabilities associated with system calls, effectively…
Best of 2024 Archives
Best of 2024 Archives Exploring the Best of 2024: Insights for Developers As we look towards the innovations and trends predicted to shape 2024, developers should be particularly attuned to…
Critical Windows Zero-Day Vulnerability Lets Attackers Steal Users NTLM Credentials
Security researchers have identified a critical zero-day vulnerability that poses a significant risk to all versions of Windows Workstation and Server, spanning from Windows 7 and Server 2008 R2 to…
Fashion-driven tech decisions
In the world of technology, trends can often dictate decisions, but following these trends without a strategic approach can lead to costly missteps. This is particularly relevant for developers grappling…