Best of 2024: Red Hat OpenShift Update Simplifies Network Edge Deployments
Red Hat has announced the general availability of its latest update to the OpenShift platform, specifically targeting the complexities associated with network edge deployments. This update carries significant implications for…
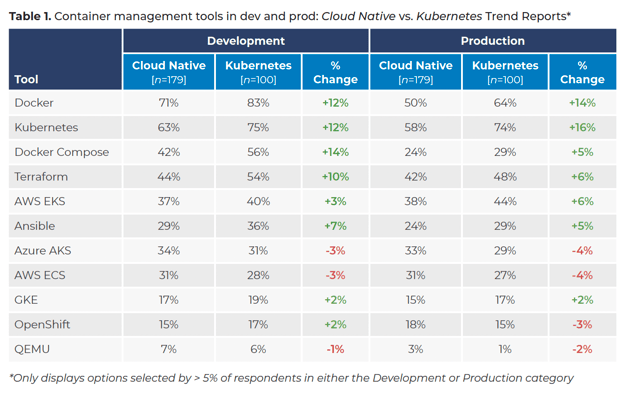
Kubernetes in 2025: Are You Ready For These Top 5 Trends & Predictions
Kubernetes in 2025: Are You Prepared for the Top 5 Trends & Predictions? As Kubernetes approaches its 10-year anniversary, its significance in the realm of cloud-native deployments is undeniable. For…
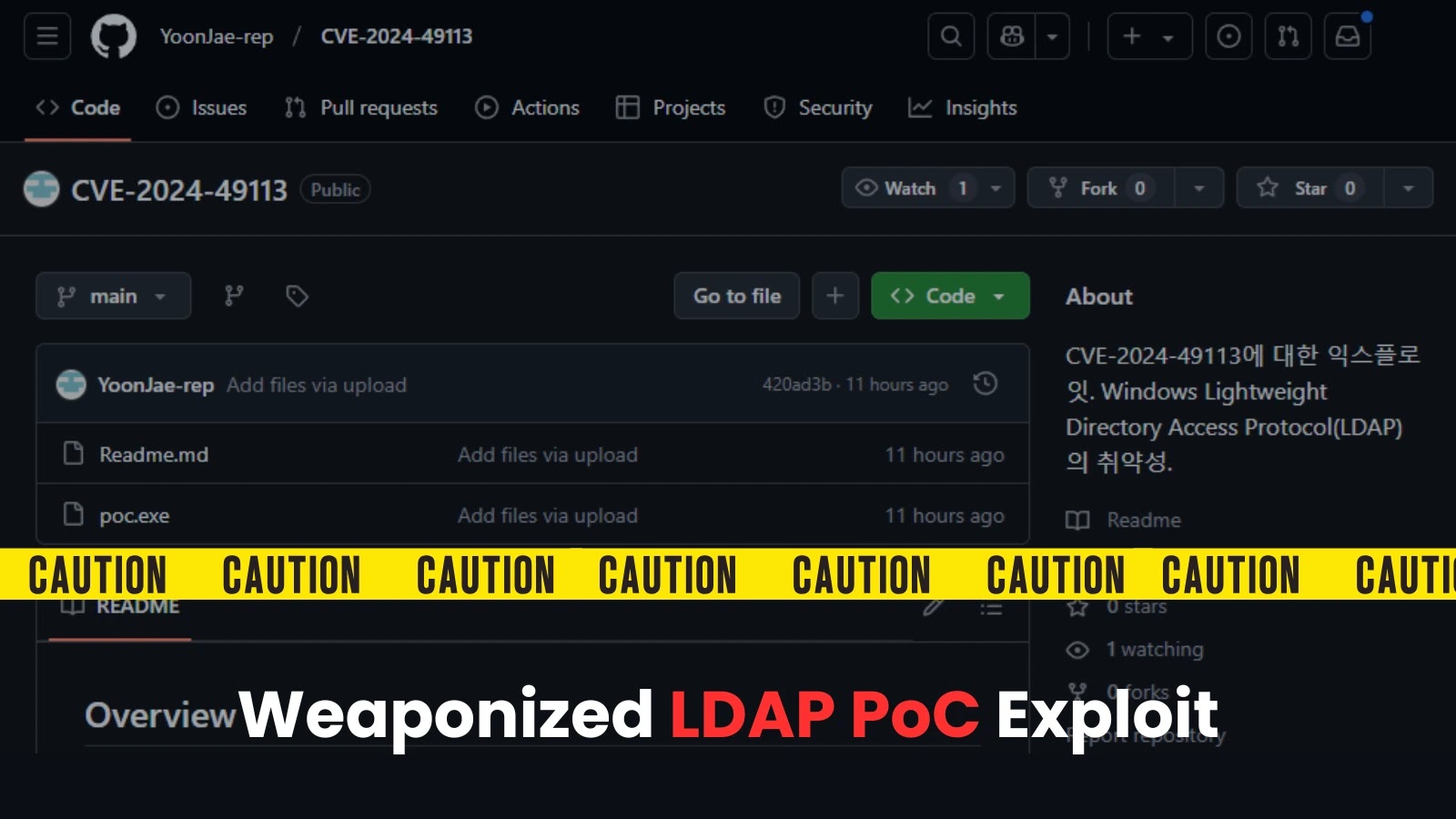
BeyondTrust Patches Critical Vulnerability Discovered During Security Incident Probe
Recently, a critical vulnerability affecting BeyondTrust’s Privileged Remote Access and Remote Support products was identified during a security incident investigation. This vulnerability poses a significant risk as it allows for…
Attack Exposure: Unpatched Cleo Managed File-Transfer Software
Attack Exposure: Unpatched Cleo Managed File-Transfer Software Security analysts have identified a critical concern for developers overseeing Cleo managed file-transfer (MFT) software. More than 200 instances of this software remain…
Watch Now: Navigating Your OT Cybersecurity Journey: From Assessment to Implementation
Navigating Your OT Cybersecurity Journey: From Assessment to Implementation In today’s digitized industrial landscape, operational technology (OT) environments face a growing array of cyber threats. For developers working in these…
BeyondTrust Issues Urgent Patch for Critical Vulnerability in PRA and RS Products
Critical Update from BeyondTrust: Urgent Patch Addresses Vulnerability in PRA and RS Products BeyondTrust has released an urgent security patch for its PowerBroker Remote Access (PRA) and Remote Support (RS)…
Multiple GStreamer Vulnerabilities Impact Linux Distributions Using GNOME
A recent analysis has identified several vulnerabilities within GStreamer, the cornerstone multimedia framework used widely in GNOME-based Linux distributions. These vulnerabilities pose real risks to developers integrating multimedia capabilities into…
Video: Hackers Bypass TSA Security with SQL Injection
Recently, a significant security breach involving the Transportation Security Administration (TSA) was exposed, highlighting vulnerabilities due to SQL injection attacks. This incident enables us to delve into how such attacks…
NetSPI Pioneers Continuous Asset Exposure Management with New External Attack Surface Management Solutions
NetSPI Enhances Continuous Asset Exposure Management with New Solutions As organizations increasingly transition to cloud-based architectures and more complex environments, the need for robust External Attack Surface Management (EASM) solutions…
Threat actors are attempting to exploit Apache Struts vulnerability CVE-2024-53677
Recent research has spotlighted the Apache Struts vulnerability CVE-2024-53677, with malicious actors actively attempting to exploit this weakness. As a developer, understanding the implications of such vulnerabilities is crucial, not…
 Exploitation of New Ivanti VPN Zero-Day Linked to Chinese Cyberspies
Exploitation of New Ivanti VPN Zero-Day Linked to Chinese Cyberspies Palo Alto Networks Patches High-Severity Vulnerability in Retired Migration Tool
Palo Alto Networks Patches High-Severity Vulnerability in Retired Migration Tool Kerio Control Firewall Vulnerability Allows 1-Click Remote Code Execution
Kerio Control Firewall Vulnerability Allows 1-Click Remote Code Execution Ivanti patches actively exploited zero-day.
Ivanti patches actively exploited zero-day. Major Vulnerabilities Patched in SonicWall, Palo Alto Expedition, and Aviatrix Controllers
Major Vulnerabilities Patched in SonicWall, Palo Alto Expedition, and Aviatrix Controllers Chinese-linked Hackers May Be Exploiting Latest Ivanti Vulnerability
Chinese-linked Hackers May Be Exploiting Latest Ivanti Vulnerability Biden’s final cyber order tackles digital weaknesses.
Biden’s final cyber order tackles digital weaknesses.