Sophos Firewall Vulnerabilities Could Allow Remote Attacks
Developers and IT security professionals utilizing Sophos firewall solutions should prioritize updating their devices following the recent announcement regarding critical security vulnerabilities. According to the vendor, these flaws can be…
Censys researchers warn 8,600 BeyondTrust instances still exposed
Censys Researchers Warn of Exposed BeyondTrust Instances Censys Researchers Warn of Exposed BeyondTrust Instances In a recent report, researchers from Censys have highlighted a significant security concern concerning over 8,600…
ASUS Routers Vulnerabilities Allows Arbitrary Code Execution
ASUS has issued a critical security advisory, drawing attention to multiple vulnerabilities present in several of its router models, which could allow for arbitrary code execution. For developers, especially those…
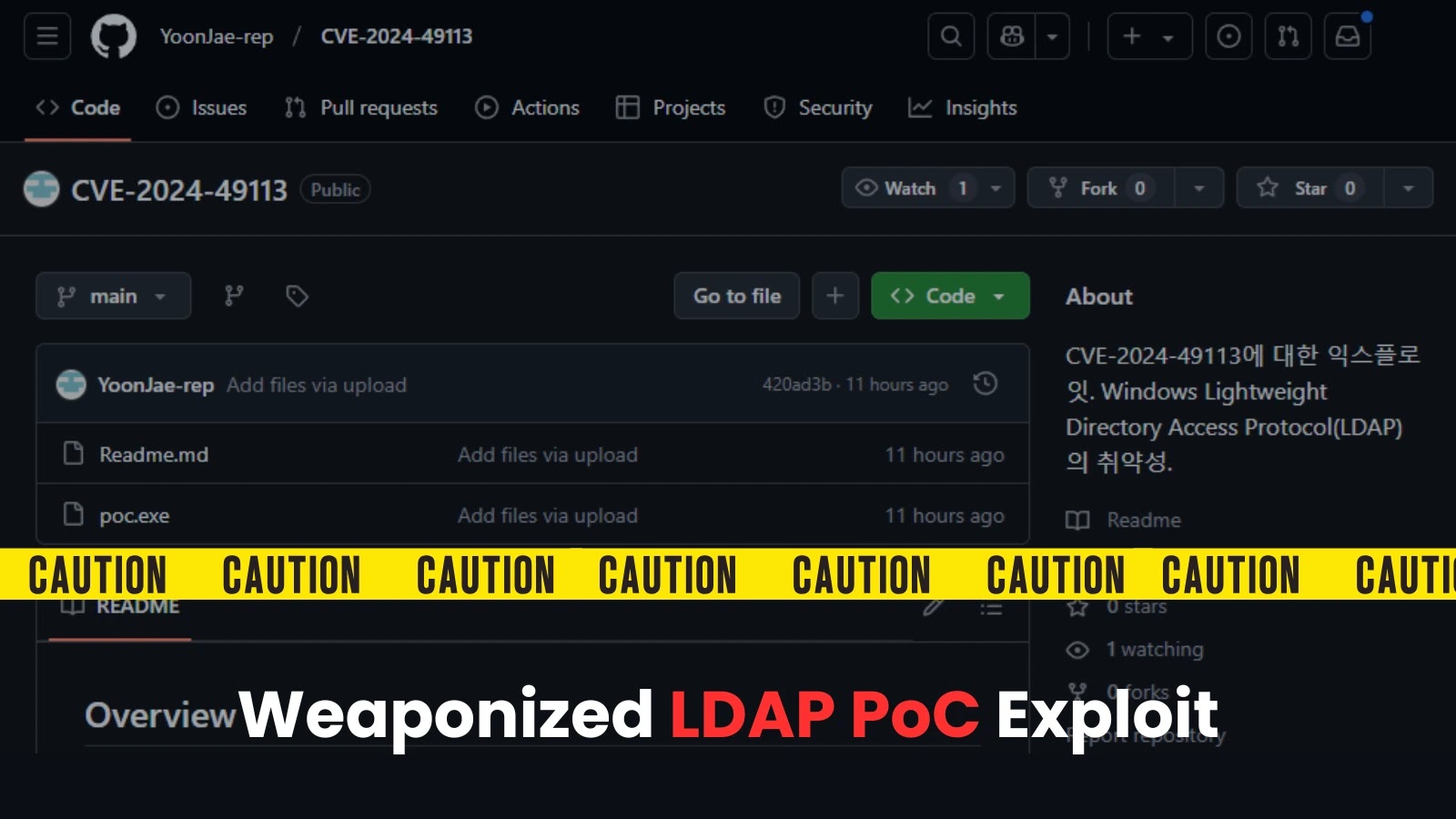
Exploit Code Published for Potentially Dangerous Windows LDAP Vulnerability
Exploit Code Published for Potentially Dangerous Windows LDAP Vulnerability The recent release of proof-of-concept (PoC) code for CVE-2024-49113 highlights a growing concern for developers working with Windows environments. This vulnerability…
2025 Forecast: AI to supercharge attacks, quantum threats grow, SaaS security woes
2025 Cybersecurity Predictions: Developer Insights on AI and Quantum Threats 2025 Cybersecurity Predictions: Developer Insights on AI and Quantum Threats As we approach 2025, cybersecurity is expected to evolve rapidly,…
Treasury hack: Lawmakers seek more details on scope, third-party vulnerabilities
The recent hack of the U.S. Treasury has raised significant concerns within the developer community regarding the cybersecurity measures established around third-party technology service providers. As agencies increasingly rely on…
Thousands of Buggy BeyondTrust Systems Remain Exposed
Researchers reveal that nearly 9,000 BeyondTrust instances remain exposed to the internet, posing significant security risks to organizations. This comes in the wake of a critical vulnerability discovery and a…
U.S. Treasury Sanctions Beijing Cybersecurity Firm for State-Backed Hacking Campaigns
U.S. Treasury Sanctions Beijing Cybersecurity Firm for State-Backed Hacking Campaigns The U.S. Treasury Department has imposed sanctions on Integrity Technology Group, a Beijing-based cybersecurity firm, due to its involvement in…
Dangerous Gmail Security Threat Confirmed But Google Won’t Fix It
As vulnerabilities within Gmail’s AI security systems become increasingly scrutinized, the question arises: why is Google hesitating to implement fixes? Here’s an analysis of the implications for developers and security…
Researchers Uncover Nuclei Vulnerability Enabling Signature Bypass and Code Execution
CVE-2024-43405, a newly identified vulnerability within Nuclei, has significant implications for developers working in security automation. This vulnerability allows attackers to bypass defined signatures, thereby enabling arbitrary code execution on…
 Exploitation of New Ivanti VPN Zero-Day Linked to Chinese Cyberspies
Exploitation of New Ivanti VPN Zero-Day Linked to Chinese Cyberspies Palo Alto Networks Patches High-Severity Vulnerability in Retired Migration Tool
Palo Alto Networks Patches High-Severity Vulnerability in Retired Migration Tool Kerio Control Firewall Vulnerability Allows 1-Click Remote Code Execution
Kerio Control Firewall Vulnerability Allows 1-Click Remote Code Execution Ivanti patches actively exploited zero-day.
Ivanti patches actively exploited zero-day. Major Vulnerabilities Patched in SonicWall, Palo Alto Expedition, and Aviatrix Controllers
Major Vulnerabilities Patched in SonicWall, Palo Alto Expedition, and Aviatrix Controllers Chinese-linked Hackers May Be Exploiting Latest Ivanti Vulnerability
Chinese-linked Hackers May Be Exploiting Latest Ivanti Vulnerability Biden’s final cyber order tackles digital weaknesses.
Biden’s final cyber order tackles digital weaknesses.