High-Severity Vulnerability Discovered In Nuclei: What You Need To Know
High-Severity Vulnerability Discovered in Nuclei: What Developers Should Know A recent finding by Wiz has uncovered a high-severity vulnerability within Nuclei, a widely used tool for security scanning and vulnerability…
AWS Repeats Same Critical RCE Vulnerability 3 Times in 4 Years
In a troubling trend that may concern developers leveraging Amazon Web Services (AWS), a critical remote code execution (RCE) vulnerability has reoccurred within AWS’s Neuron SDK three times over the…
Only 26% of Europe’s top companies earn a high rating for cybersecurity
Only 26% of Europe’s Top Companies Achieve High Cybersecurity Ratings According to a recent analysis by SecurityScorecard, a troubling trend has emerged in the realm of cybersecurity across Europe’s top…
Open source vulnerability scanner found with a serious vulnerability in its own code
Open Source Vulnerability Scanner Nuclei Exposed to Serious Flaw Recent developments have revealed a critical vulnerability in Nuclei, a popular open-source vulnerability scanner widely used by developers to find and…
“Bad Likert Judge” – New Technique to Jainbreak AI Using LLM Vulnerabilities
A recent breakthrough in the realm of AI text generation has emerged, with researchers unveiling a novel technique known as the Bad Likert Judge. This method specifically targets and exploits…
Cybersecurity in 2025: A Look Back at 2024’s Biggest Cyber Attacks & Lessons for the Future – SOCRadar® Cyber Intelligence Inc.
As we transition into 2025, it’s crucial for developers to reflect on the major cyber attacks that occurred in 2024. Understanding these incidents not only allows for enhanced cybersecurity measures…
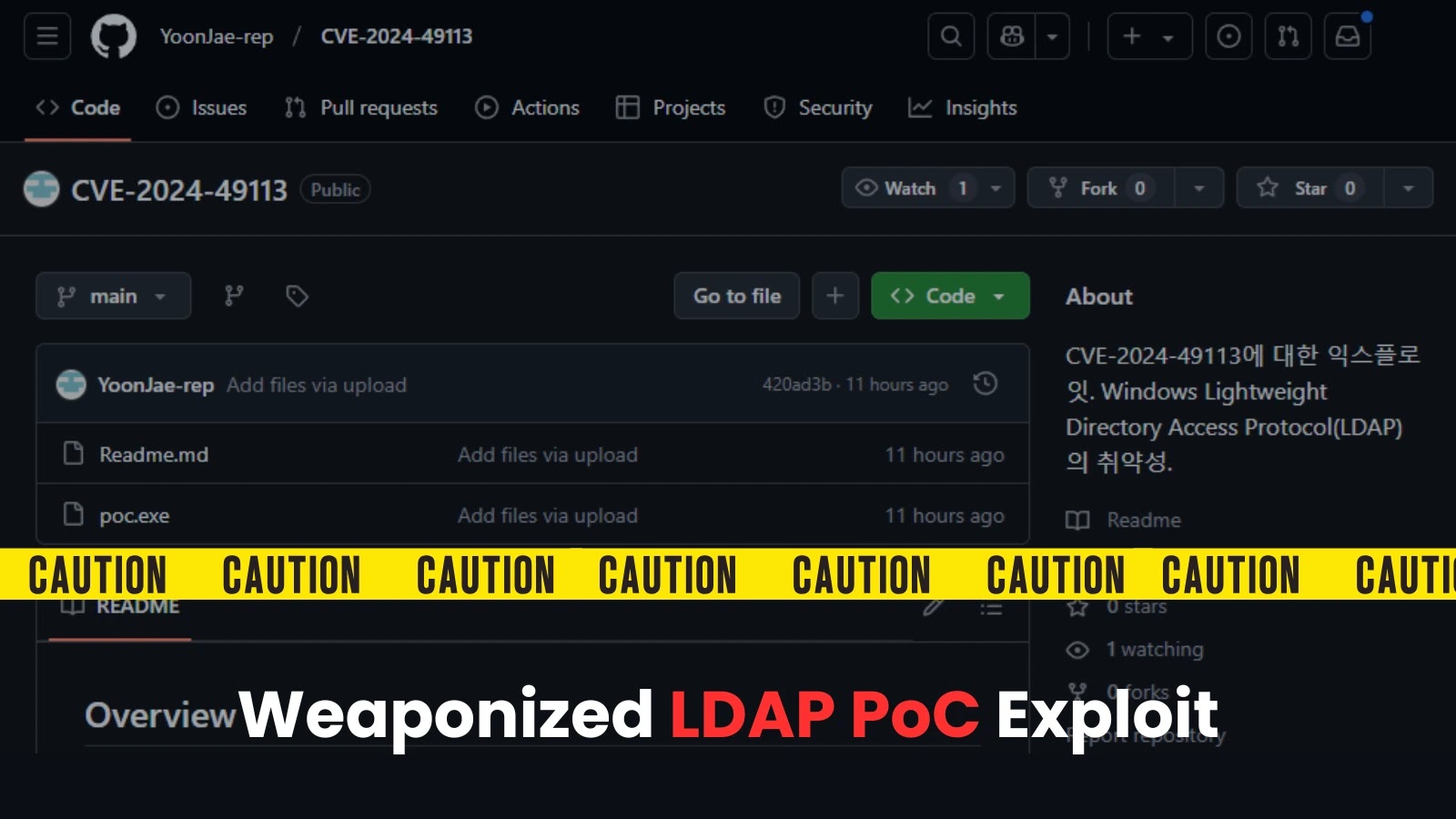
New Hack Threatens New York Internet Users
A newly discovered web security vulnerability is causing concern for internet users, particularly in New York, as it poses significant risks that developers need to be aware of. This vulnerability,…
PoC Exploit Released For OpenSSH Arbitrary Code Execution Vulnerability
A critical vulnerability in OpenSSH, designated as CVE-2024-6387 and informally referred to as regreSSHion, has been flagged as a significant risk. A proof-of-concept (PoC) exploit is now in circulation, prompting…
The true cost of a security breach
The True Cost of a Security Breach The Hidden Toll of Security Incidents Security breaches have become an all-too-frequent headline in our digital landscape, and as developers, understanding their true…
From $22M in Ransom to +100M Stolen Records: 2025’s All-Star SaaS Threat Actors to Watch
SaaS threats significantly escalated in 2024, showcasing a pressing need for developers to reassess security protocols and integration practices. With 7,000 password attacks occurring every second, an alarming 58% increase…
 Exploitation of New Ivanti VPN Zero-Day Linked to Chinese Cyberspies
Exploitation of New Ivanti VPN Zero-Day Linked to Chinese Cyberspies Palo Alto Networks Patches High-Severity Vulnerability in Retired Migration Tool
Palo Alto Networks Patches High-Severity Vulnerability in Retired Migration Tool Kerio Control Firewall Vulnerability Allows 1-Click Remote Code Execution
Kerio Control Firewall Vulnerability Allows 1-Click Remote Code Execution Ivanti patches actively exploited zero-day.
Ivanti patches actively exploited zero-day. Major Vulnerabilities Patched in SonicWall, Palo Alto Expedition, and Aviatrix Controllers
Major Vulnerabilities Patched in SonicWall, Palo Alto Expedition, and Aviatrix Controllers Chinese-linked Hackers May Be Exploiting Latest Ivanti Vulnerability
Chinese-linked Hackers May Be Exploiting Latest Ivanti Vulnerability Biden’s final cyber order tackles digital weaknesses.
Biden’s final cyber order tackles digital weaknesses.