Rockstar 2FA: Phishing-as-a-Service Threatens Microsoft 365 Credentials through AiTM Attacks
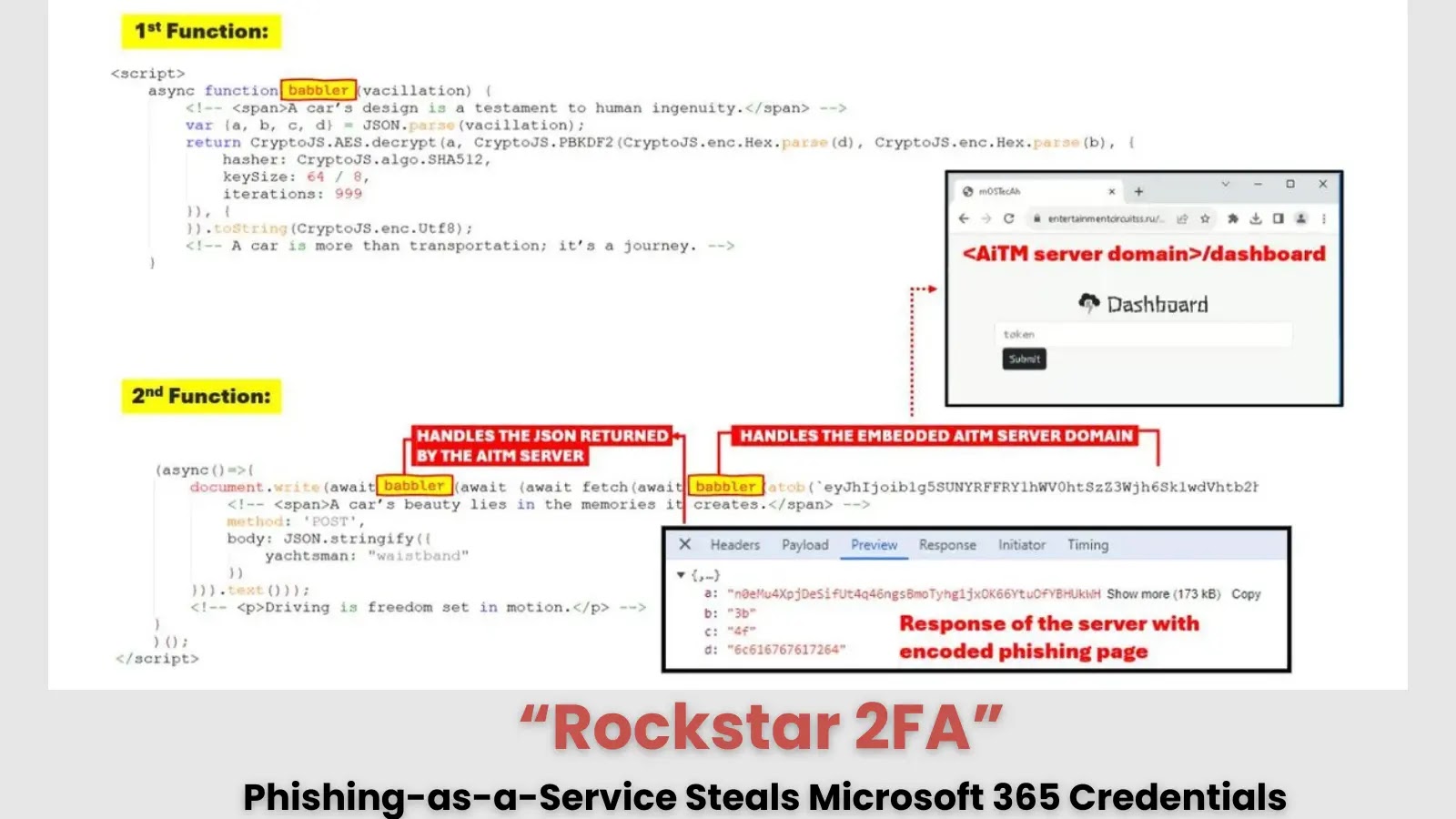
In the evolving landscape of cybersecurity threats, developers must take heed of the emergence of ‘Rockstar 2FA’, a sophisticated phishing kit that has become notorious for its capability to harvest Microsoft 365 credentials through advanced Account take over Methods, commonly referred to as AiTM attacks. This tool exemplifies how malicious actors are leveraging technology to automate and scale their phishing operations.
The Rockstar 2FA phishing kit allows cybercriminals to create counterfeit login screens that mimic legitimate Microsoft 365 interfaces. By integrating a two-factor authentication (2FA) process, the attackers can trick users into entering their credentials and subsequent authentication codes, thereby compromising accounts. For developers, understanding these tactics can provide crucial insights into enhancing the security measures of applications they build. References to official resources, such as Microsoft’s documentation on secure application design, can be an essential read for developers looking to fortify their systems against such threats. You can find more about secure coding practices here.
Moreover, the rise of phishing-as-a-service models underscores the necessity for developers to implement comprehensive validation processes for user input and authentication flows. By utilizing techniques such as OAuth for authorization and employing strict content security policies (CSPs), developers can create a more resilient application architecture that mitigates the risk of falling victim to similar attack vectors. The importance of educating users about phishing threats cannot be overstated; simple user awareness programs can serve as an essential line of defense.
As phishing methods continue to grow more sophisticated, it is critical for developers to stay updated on the latest trends and attack methodologies. Industry experts are predicting an uptick in the utilization of such tools, especially as more organizations migrate to cloud services like Microsoft 365. This shift presents developers with a unique opportunity to innovate security practices and educate end-users on identifying suspicious activities. Resources for building more secure applications can be found in the OWASP Top Ten, which highlights common vulnerabilities and mitigation strategies.
In conclusion, the proliferation of tools like Rockstar 2FA signifies a pressing challenge for developers focused on cybersecurity. By actively monitoring these trends and embedding robust security practices within their workflows, developers can contribute to a more secure digital ecosystem.



