As developers, it is crucial to recognize the implications of misconfigured RBAC in cloud-native environments, specifically within Kubernetes clusters deployed in platforms such as Azure. Properly implemented, RBAC helps enforce the principle of least privilege, ensuring that users and services only have permissions necessary to perform their tasks. However, when configurations are lax or improperly defined, attackers can exploit these weaknesses to gain broader access across the cluster.
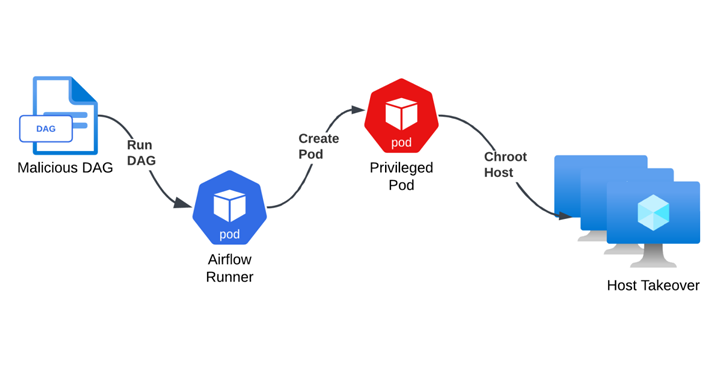
For instance, if a developer inadvertently grants excessive permissions to a service account within an Azure Airflow deployment, it could potentially allow an attacker to compromise not only the Airflow instance but also reach sensitive Kubernetes resources or even root virtual machine access. Such incidents could lead to significant disruptions, including unauthorized data access and manipulation, which could have far-reaching consequences for organizations that depend on these technologies.
To mitigate these risks, developers should adopt best practices around RBAC definitions:
1. **Review Roles Regularly**: Conduct regular audits of defined roles to ensure they align with current operational needs.
2. **Implement Fine-Grained Access Control**: Use the principle of least privilege when assigning roles, restricting access strictly to what is necessary for functionality.
3. **Leverage Namespaces for Segmentation**: Utilize Kubernetes namespaces effectively to isolate resources and enforce security boundaries.
Real-world scenarios show that companies are increasingly adopting more stringent security practices as part of their DevSecOps approach, reflecting a growing awareness of the need for robust access control mechanisms. As the industry shifts towards more integrated cloud solutions, configuration management tools—like Terraform or Helm—should be employed for deploying and managing Kubernetes clusters to ensure configurations are repeatable and auditable.
To further enhance your security posture, stay informed about the latest Kubernetes security updates and subscribe to alerts from the [Kubernetes Security Special Interest Group](https://kubernetes.io/community/groups/#security). Following community discussions can also provide insights into security vulnerabilities and mitigation strategies.
Looking forward, we predict that the emphasis on security in development workflows will continue to grow, especially with an increase in regulatory scrutiny and compliance requirements demanding organizations to maintain not only functionality but also security in their applications.
By paying close attention to RBAC configurations within Azure Airflow and similar deployments, developers can prevent potential exploits and contribute to a more secure cloud environment.




