For instance, in the realm of web development, one of the newly reported vulnerabilities pertains to a popular content management system utilized by numerous developers worldwide. Such systems often become targets due to their widespread adoption. Developers integrating this technology into their workflows should ensure they regularly consult CISA’s catalog and keep abreast of patches released by the vendor. Regularly updating libraries and dependencies not only adheres to the Shift Left security approach but also preemptively mitigates risks associated with known vulnerabilities.
Moreover, the landscape of application security is evolving to incorporate more automation tools such as Static Application Security Testing (SAST) and Dynamic Application Security Testing (DAST) frameworks. These tools can significantly aid developers in detecting vulnerabilities within the development lifecycle, enabling quicker remediation. For developers working in continuous integration/continuous deployment (CI/CD) environments, integrating these security checks can provide real-time feedback and maintain a robust security posture across all stages of development.
As threats become more sophisticated, the trend of utilizing threat intelligence solutions is also on the rise. By leveraging such tools, developers can gain insights into emerging vulnerabilities and exploit patterns. This proactive measure allows development teams to adjust their security strategies accordingly and prioritize patches based on exploitability in the wild.
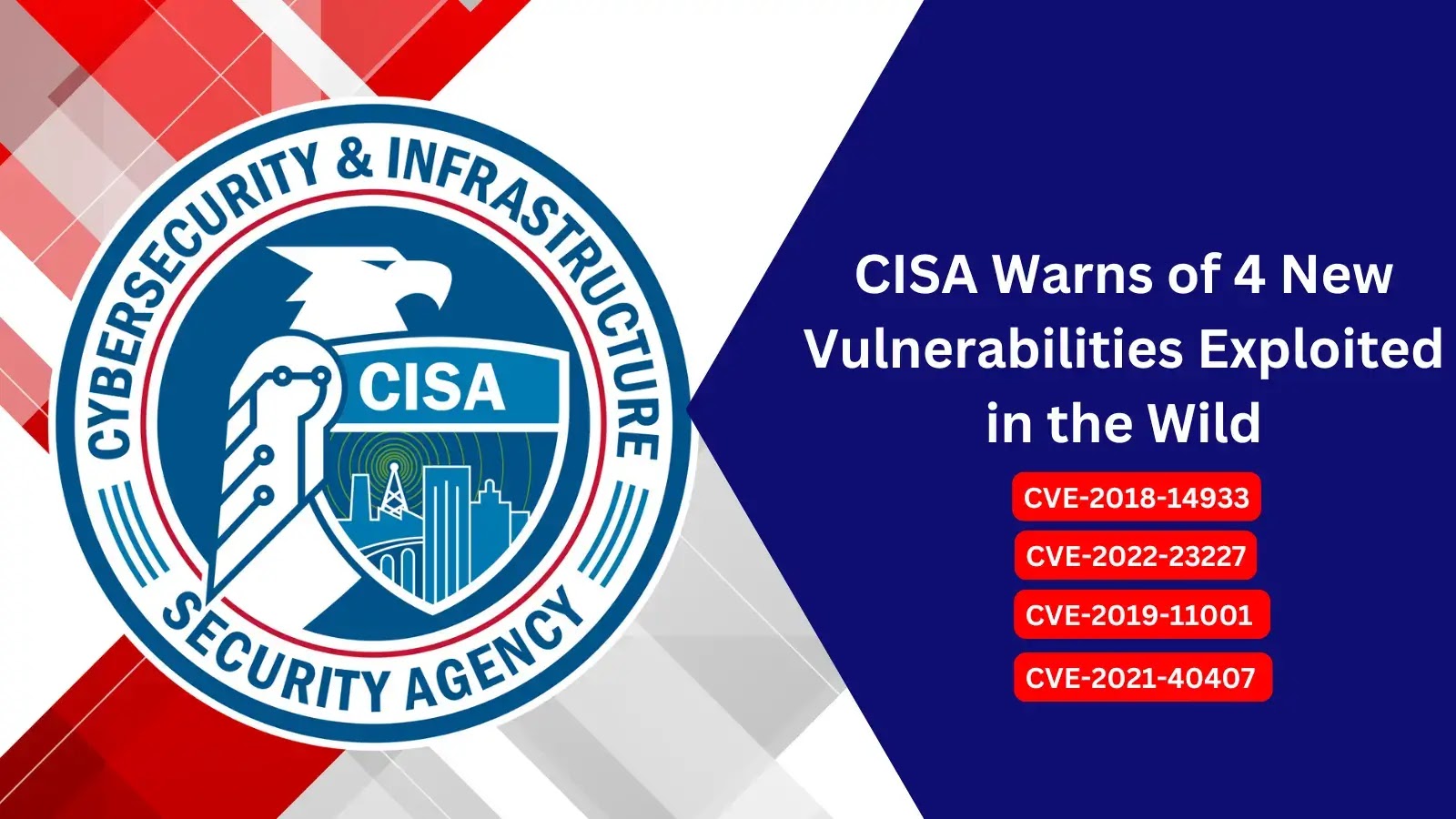
To assist developers in navigating these vulnerabilities, CISA provides comprehensive resources and documentation. For a deeper understanding of specific vulnerabilities and recommended mitigations, developers can visit the official CISA page at [CISA Known Exploited Vulnerabilities](https://www.cisa.gov/known-exploited-vulnerabilities-catalog) and ensure their applications remain secure against potential breaches.
In conclusion, as more vulnerabilities come to light, developers must prioritize security in their coding practices, continuously educate themselves on emerging threats, and utilize available resources to safeguard their applications.



