Emerging QR Code-Based Command and Control Attacks: Implications for Developers
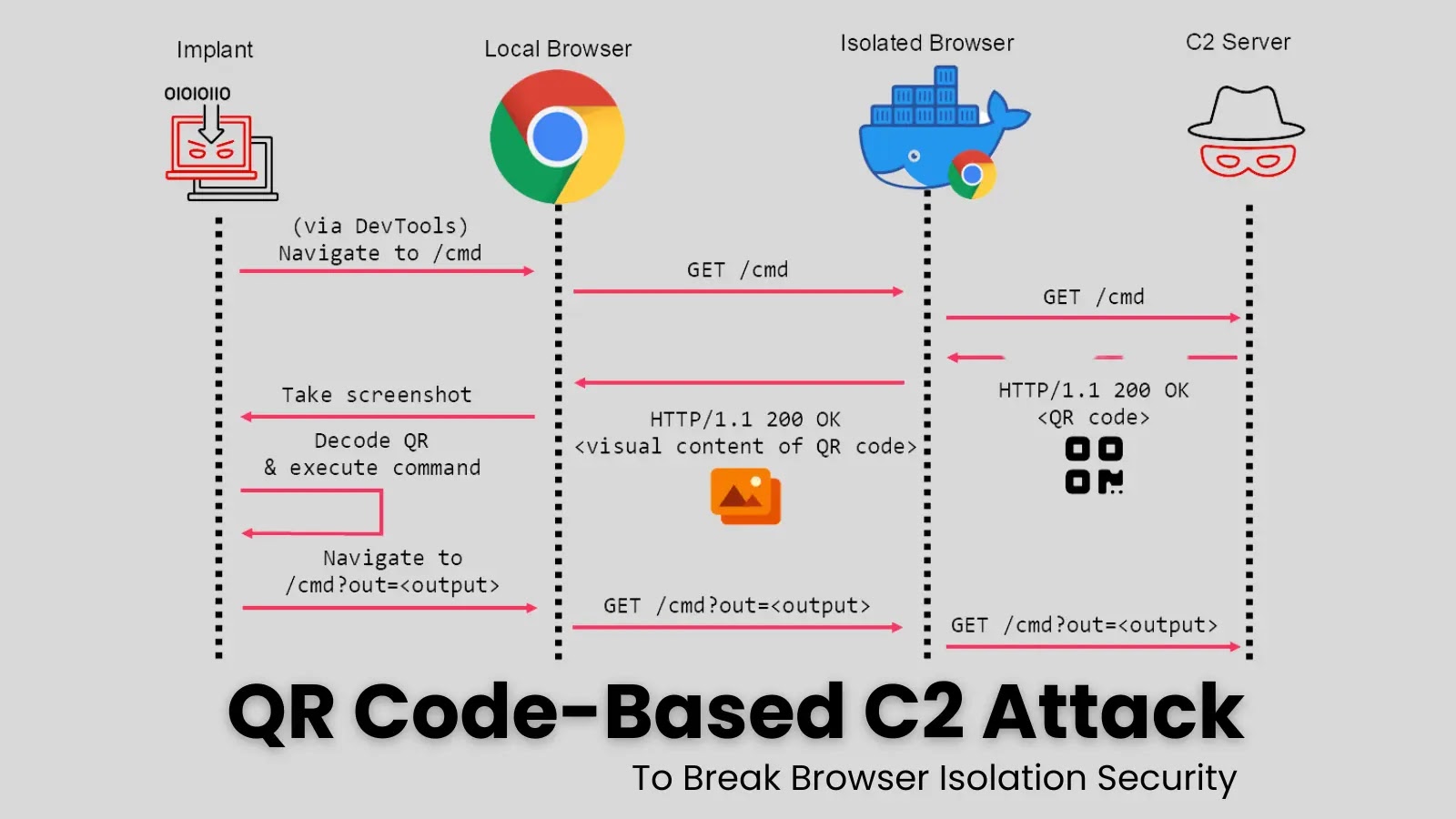
Mandiant, a leading cybersecurity firm, has recently uncovered a novel attack vector that leverages QR codes to compromise browser isolation security technologies. This development raises significant concerns for developers responsible for maintaining robust cybersecurity protocols in their applications.
As developers, understanding the mechanics of such attacks can directly influence how we design and implement security frameworks within our tools and applications. The QR code-based Command and Control (C2) attack enables malicious actors to bypass isolation measures traditionally used to protect sensitive browsing sessions. This tactic emphasizes the need for developers to rethink the security layers they integrate into web applications and services.
Historically, browser isolation technologies have acted as a barrier between untrusted web content and a user’s local environment. However, this new attack method cleverly exploits the inherent trust users place in QR codes, which can be easily scanned and executed by mobile or desktop devices. For example, developers integrating QR code functionality in applications or marketing tools should ensure that scanning leads to verified, secure destinations only.
In practical terms, developers are encouraged to implement stringent validation checks for any QR code-derived URLs. This could include mechanisms to check that the destination website aligns with known-safe domains or utilizes robust authentication methods. Additionally, employing techniques such as Content Security Policy (CSP) could help in mitigating the risks posed by malicious QR codes leading users to compromised websites.
As we continue to see trends indicating that attackers will increasingly leverage social engineering and easily accessible technology like QR codes, the integration of adaptive defense strategies will be crucial. Future-proofing applications may involve real-time monitoring systems that can analyze traffic patterns for unusual behaviors indicative of QR-based exploitation.
For developers looking to bolster their understanding of securing against such vulnerabilities, resources like the OWASP Top Ten provide essential insights into current security risks in web applications. Furthermore, adopting frameworks that prioritize security, such as those outlined in the Common Weakness Enumeration, will help developers maintain high security standards.
In conclusion, the emergence of QR code-based C2 attacks is a call to action for developers to integrate comprehensive security measures early in the application lifecycle. By adapting existing practices and keeping abreast of the latest threats, developers can strengthen their applications against this evolving landscape of cyber threats.



