“`html
APT-C-60 Exploits WPS Office Vulnerability to Deploy SpyGlace Backdoor

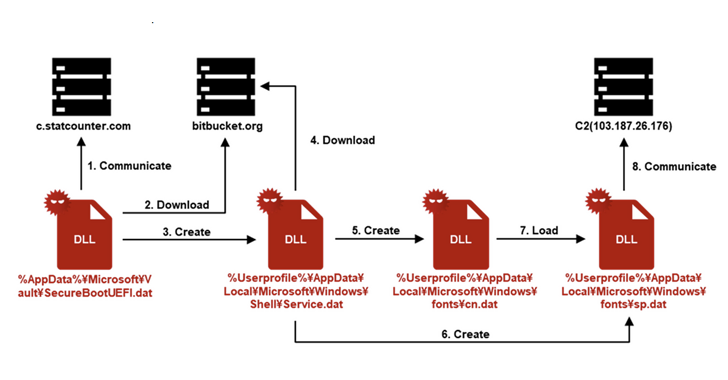
In an alarming development within the cybersecurity landscape, the advanced persistent threat group known as APT-C-60 has leveraged a vulnerability in WPS Office to deploy the SpyGlace backdoor. This incident underscores the need for developers to prioritize security in their software development lifecycle.
APT-C-60’s method involves selective phishing campaigns that exploit the weaknesses within WPS Office. Taking note of this tactic, developers should incorporate threat modeling techniques, such as the OWASP Threat Modeling Framework, into their workflows. By proactively identifying potential weaknesses in their applications, teams can bolster defenses before malicious actors have a chance to exploit them.
The incident notably targets users in Japan, employing sophisticated techniques that highlight a growing trend towards region-specific attacks. As developers, it’s essential to stay informed about geographical fraud trends. Tools like Censys can assist in monitoring the exposure of your applications across various regions, ensuring that you can respond effectively to localized threats.
To reinforce the security frameworks surrounding application development, developers should consider making use of code analysis tools that can identify vulnerabilities in third-party libraries, particularly those used for document processing, as highlighted by this exploit. Resources such as the Snyk documentation can provide guidance on integrating security testing directly into CI/CD pipelines, allowing for real-time feedback on code vulnerabilities.
This incident serves as a stark reminder of the evolving nature of cyber threats – a trend likely to continue as we advance into the next decade. Developers should anticipate increasingly sophisticated attacks and devote time to education on emerging security protocols. The best practice remains to implement a principle of ‘secure by design’, where security is not an addon but a foundational element throughout the software development process.
In summary, developers should take heed of the APT-C-60 exploit to improve their application security measures, adopt proactive cybersecurity strategies, and integrate relevant tools and practices into their development workflows. By staying vigilant and informed, developers can play a crucial role in mitigating the risks posed by such advanced threats.



